Your Ranked vulnerability risk worksheet images are available in this site. Ranked vulnerability risk worksheet are a topic that is being searched for and liked by netizens today. You can Get the Ranked vulnerability risk worksheet files here. Download all royalty-free photos.
If you’re searching for ranked vulnerability risk worksheet images information linked to the ranked vulnerability risk worksheet topic, you have visit the right site. Our website always gives you suggestions for viewing the highest quality video and image content, please kindly hunt and locate more informative video content and graphics that match your interests.
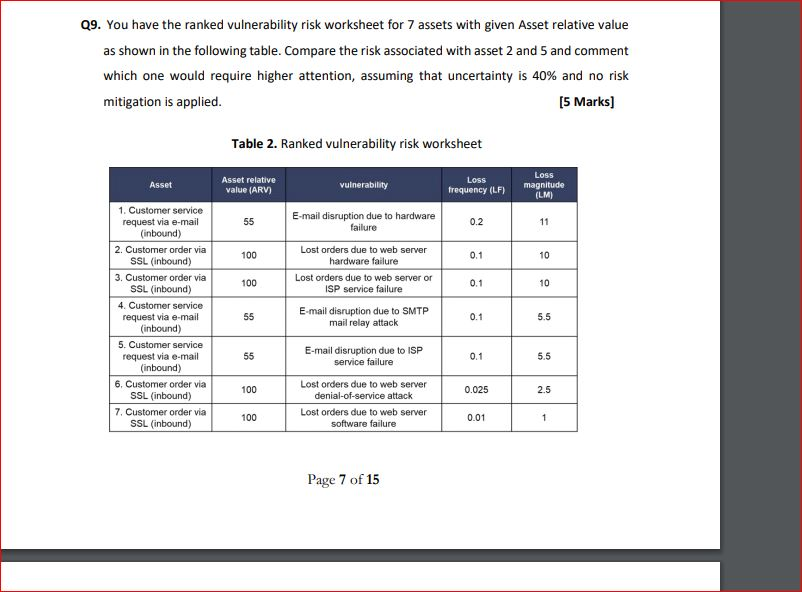
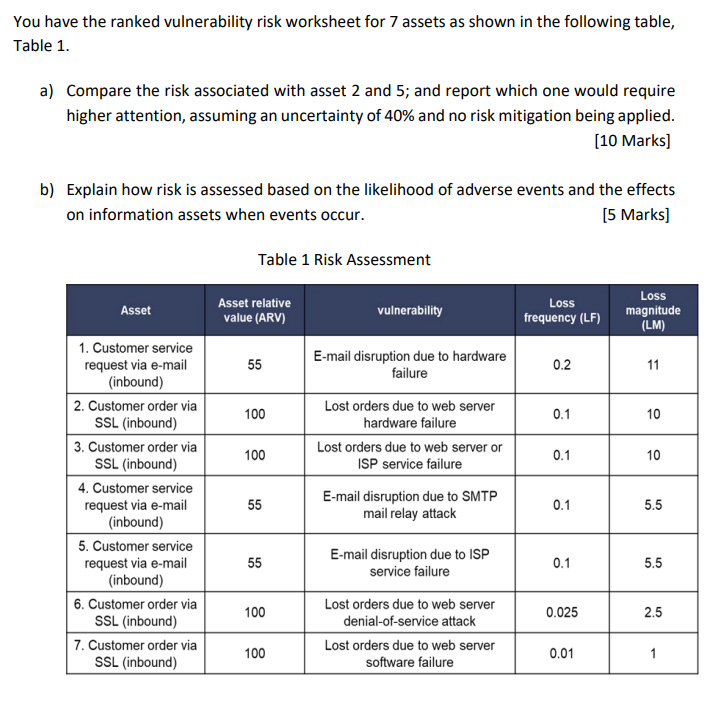
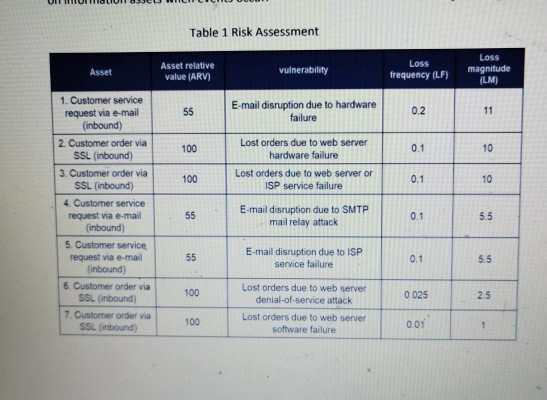
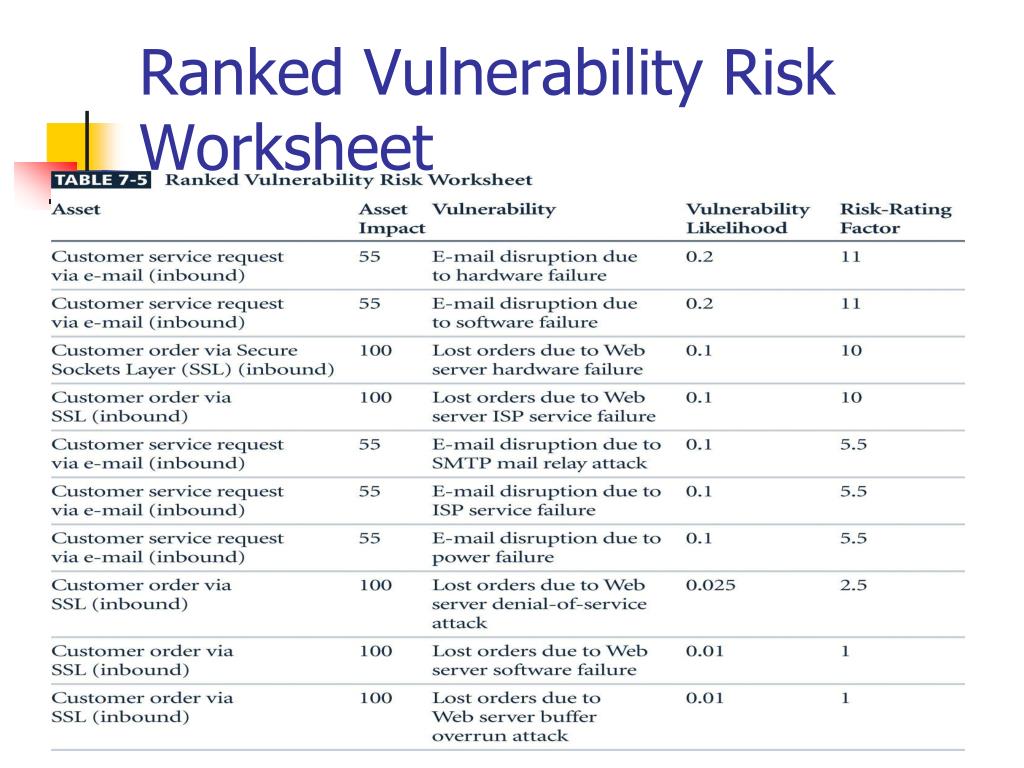
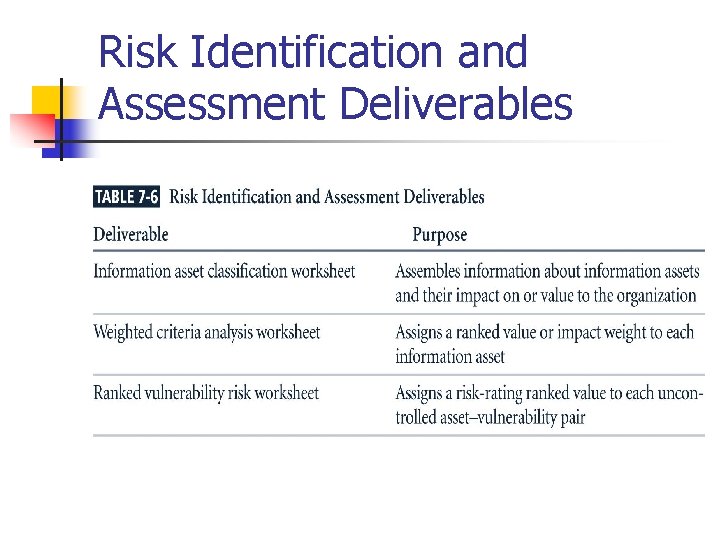
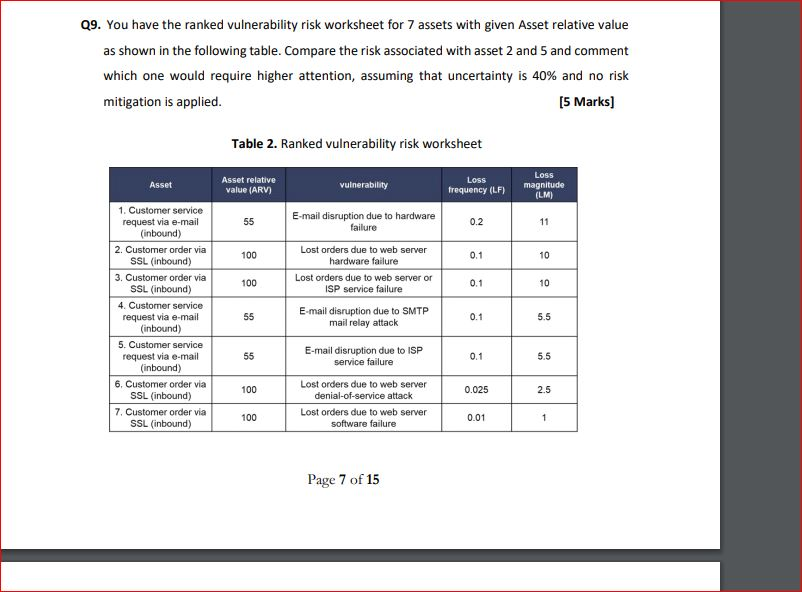
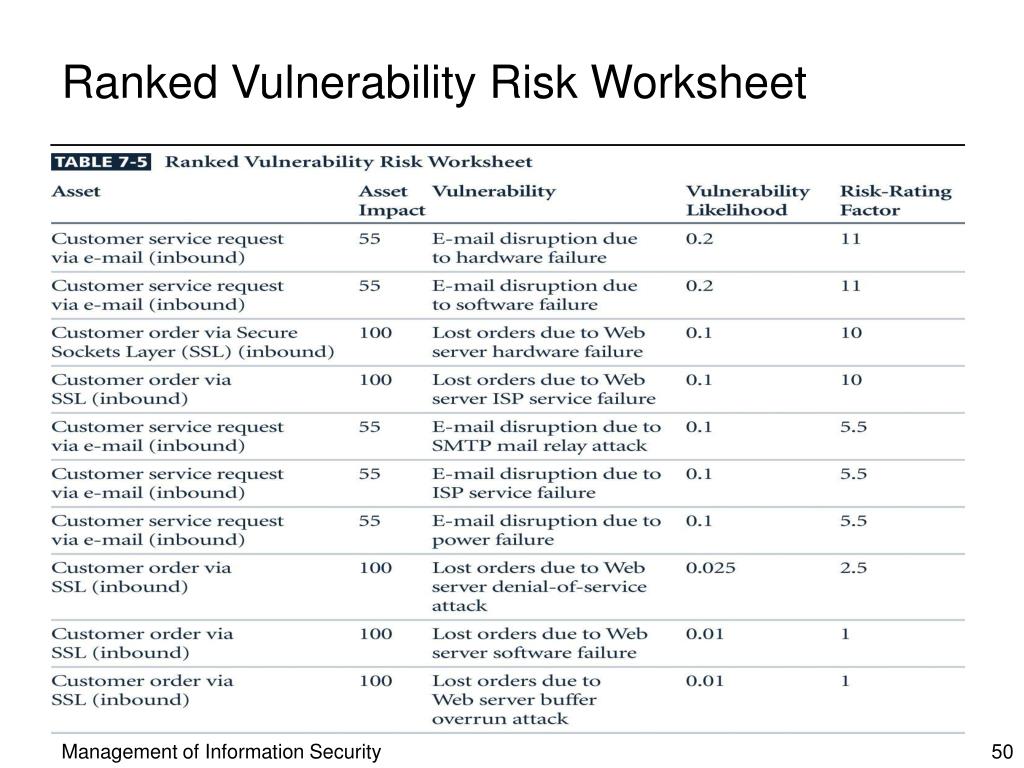
Ranked Vulnerability Risk Worksheet. Ranked Vulnerability Risk worksheet assigns a risk-rating ranked value to each uncontrolled asset-vulnerability pairThis worksheet is the initial working document for assessing and controlling risks. Compare the risk associated with asset 2 and 5 and comment which one would require higher attention assuming that uncertainty is 40 and no risk mitigation is applied. Remains even after current control has been applied. Documenting the Results of Risk Assessment.
 29 You Have The Ranked Vulnerability Risk Worksheet Chegg Com From chegg.com
29 You Have The Ranked Vulnerability Risk Worksheet Chegg Com From chegg.com
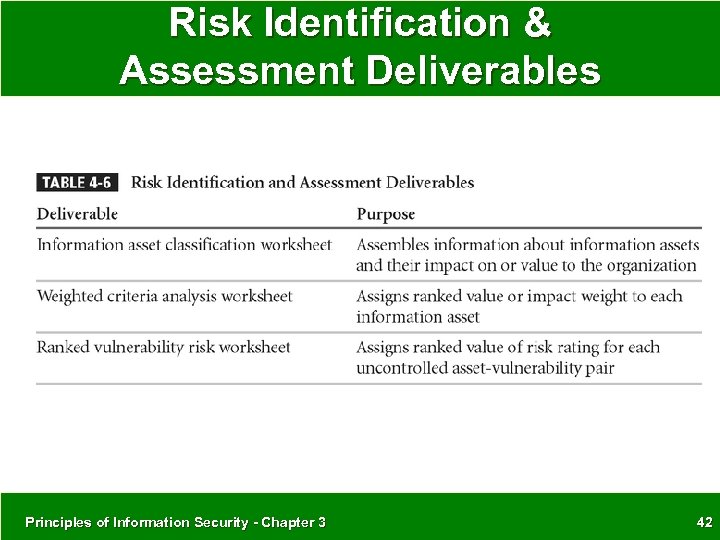
Mission of the business asset inventory weighted factor analysis worksheet ranked vulnerability risk worksheet risk strategies and control justification. Table 3351 Ranked vulnerability risk worksheet. Get thousands of teacher-crafted activities that sync up with the school year. What are the deliverables from this stage of the risk management project. The final summarized document is the ranked vulnerability risk worksheet. Compare the risk associated with asset 2 and 5 and comment which one would require higher attention assuming that uncertainty is 40 and no risk mitigation is applied.
Attempts to prevent the exploitation of the vulnerability-this is the preferred approach.
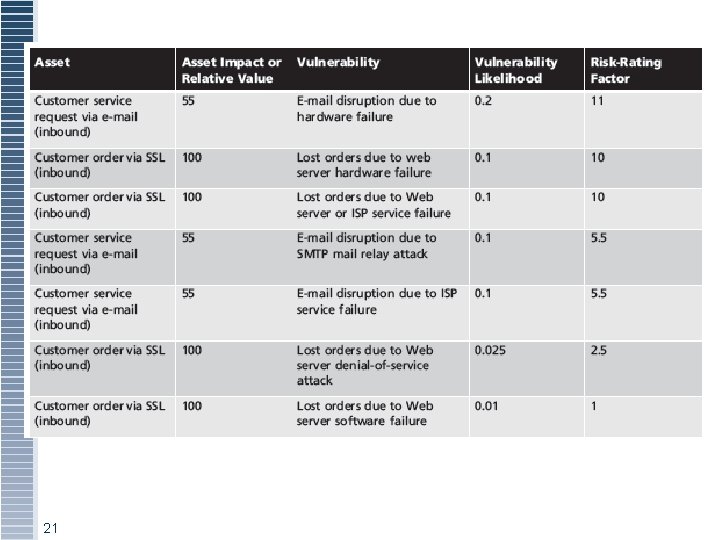
The final summarized document is the ranked vulnerability risk worksheet a sample of which is shown in the following table. Threat Risk Priority Rank Vulnerabilities Countermeasures Cost Probability Criticality Total Security Assessment Worksheet. 39 Ranked Vulnerability Risk Worksheet Asset Asset Impact Vulnerability Vulnerability Likelihood Risk-Rating Factor Customer service request via e-mail inbound 55 E-mail disruption due to hardware failure 02 11 Customer service request via e-mail inbound 55 E-mail disruption due to software failure 02 11 Customer order via SSL inbound. Get thousands of teacher-crafted activities that sync up with the school year. The risk identification process should designate what function the. Ad The most comprehensive library of free printable worksheets digital games for kids.
 Source: slidetodoc.com
Source: slidetodoc.com
Asset AI Vulnerability VL Risk rating factor e. The final summarized document is the ranked vulnerability risk worksheet a sample of which is shown in the following table. Asset AI Vulnerability VL Risk rating factor e. The final summarized document is the ranked vulnerability risk worksheet. Documenting the Results of Risk Assessment.

The final summarized document is the ranked vulnerability risk worksheet a sample of which is shown in the following table. You can begin with the columns from the Ranked Vulnerability Risk worksheet Asset Impact Vulnerability Likelihood determine the risk rating and then include percentage of current control and the uncertainty rate to come up with a final risk -rating estimate. Rank possible hazards based on frequency and severity of risk 1. Using the Web search for at least three tools to automate risk assessment. 51 Introduction The primary goal of risk control is to reduce risk to an acceptable level What level is acceptable.
 Source: chegg.com
Source: chegg.com
Risk Assessment Worksheet Asset Undesirable EventImpact Ling. Threat Risk Priority Rank Vulnerabilities Countermeasures Cost Probability Criticality Total Security Assessment Worksheet. Ranking Hazards STEP 2 TASK B. What are the deliverables from this stage of the risk management project. Ad The most comprehensive library of free printable worksheets digital games for kids.

It is impossible to design and deploy a totally risk-free environment Risk control is often achieved by applying. Collect information on automated risk assessment tools. Risk Assessment Worksheet Asset Undesirable EventImpact Ling. Remains even after current control has been applied. Ranked Vulnerability Risk worksheet assigns a risk-rating ranked value to each uncontrolled asset-vulnerability pairThis worksheet is the initial working document for assessing and controlling risks.

The risk identification process should designate what function the. Get thousands of teacher-crafted activities that sync up with the school year. Columns are completed during each step of the risk management process. The final summarized document is the ranked vulnerability risk worksheet. Attempts to prevent the exploitation of the vulnerability-this is the preferred approach.
 Source: present5.com
Source: present5.com
Both the TVA and Ranked Vulnerability Risk worksheet are tools that are used as risk identification and assessment deliverables. Generate the ranked vulnerability risk worksheet for the asset selected in part c. Asset Inventory Refer to. And report which one would require higher attention assuming an uncertainty of 40 and no risk mitigation being applied. Cite your references for the vulnerability likelihood estimates if any applies.
 Source: chegg.com
Source: chegg.com
Generate the ranked vulnerability risk worksheet for the asset selected in part c. Get thousands of teacher-crafted activities that sync up with the school year. You have the ranked vulnerability risk worksheet for 7 assets as shown in the following table Table 1. Managing Vulnerabilities and Applying Countermeasures Paper. Table 3351 Ranked vulnerability risk worksheet.
 Source: slideserve.com
Source: slideserve.com
SEC401 Version 2 1. Generate the ranked vulnerability risk worksheet for the asset selected in part c. Remains even after current control has been applied. Ad The most comprehensive library of free printable worksheets digital games for kids. Mission of the business asset inventory weighted factor analysis worksheet ranked vulnerability risk worksheet risk strategies and control justification.

Table 3351 Ranked vulnerability risk worksheet. Threat and Risk Assessment Paper. Get thousands of teacher-crafted activities that sync up with the school year. The final summarized document is the ranked vulnerability risk worksheet a sample of which is shown in the following table. Mission of the business asset inventory weighted factor analysis worksheet ranked vulnerability risk worksheet risk strategies and control justification.
 Source: expertsmind.com
Source: expertsmind.com
The recognition enumeration and documentation of risks to an organizations information assets. Remains even after current control has been applied. Once ranked vulnerability risk worksheet is complete must choose one of five strategies to control each risk-defend-transfer-mitigate-accept-terminate. Create a ranked list of risk associated with the four vulnerabilities. It is impossible to design and deploy a totally risk-free environment Risk control is often achieved by applying.
 Source: slidetodoc.com
Source: slidetodoc.com
The recognition enumeration and documentation of risks to an organizations information assets. Table 3351 Ranked vulnerability risk worksheet. Risk Assessment Worksheet Asset Undesirable EventImpact Ling. Ranking Hazards STEP 2 TASK B. Ad The most comprehensive library of free printable worksheets digital games for kids.
 Source: brainkart.com
Source: brainkart.com
Managing Vulnerabilities and Applying Countermeasures Paper. What are the deliverables from this stage of the risk management project. Documenting the Results of Risk Assessment. A Compare the risk associated with asset 2 and 5. Threat Risk Priority Rank Vulnerabilities Countermeasures Cost Probability Criticality Total Security Assessment Worksheet.

51 Introduction The primary goal of risk control is to reduce risk to an acceptable level What level is acceptable. You have the ranked vulnerability risk worksheet for 7 assets with given Asset relative value as shown in the following table. 39 Ranked Vulnerability Risk Worksheet Asset Asset Impact Vulnerability Vulnerability Likelihood Risk-Rating Factor Customer service request via e-mail inbound 55 E-mail disruption due to hardware failure 02 11 Customer service request via e-mail inbound 55 E-mail disruption due to software failure 02 11 Customer order via SSL inbound. Table 3351 Ranked vulnerability risk worksheet. You have the ranked vulnerability risk worksheet for 7 assets as shown in the following table Table 1.
 Source: chegg.com
Source: chegg.com
Generate the ranked vulnerability risk worksheet for the asset selected in part c. Cite your references for the vulnerability likelihood estimates if any applies. Generate the ranked vulnerability risk worksheet for the asset selected in part c. Managing Vulnerabilities and Applying Countermeasures Paper. Ad The most comprehensive library of free printable worksheets digital games for kids.
 Source: slidetodoc.com
Source: slidetodoc.com
Refer to Risk Ranking Measures handoutworksheet. Using the hazards from Task A talk to state and local emergency management EM depart-ments the local fire department and other experts in your community state or region about the frequency and severity of risks. Threat and Risk Assessment Paper. Compare the risk associated with asset 2 and 5 and comment which one would require higher attention assuming that uncertainty is 40 and no risk mitigation is applied. Create a ranked list of risk associated with the four vulnerabilities.
 Source: slideserve.com
Source: slideserve.com
Documenting the Results of Risk Assessment. Using the hazards from Task A talk to state and local emergency management EM depart-ments the local fire department and other experts in your community state or region about the frequency and severity of risks. Remains even after current control has been applied. Compare the risk associated with asset 2 and 5 and comment which one would require higher attention assuming that uncertainty is 40 and no risk mitigation is applied. Study Material Lecturing Notes Assignment Reference Wiki description explanation brief detail.
 Source: slidetodoc.com
Source: slidetodoc.com
Risk Assessment Worksheet Once the impact of an undesirable event is defined create a worksheet for organizing and later analyzing the information. Create a ranked list of risk associated with the four vulnerabilities. Ranked vulnerability risk worksheet. Generate the ranked vulnerability risk worksheet for the asset selected in part c. Cite your references for the vulnerability likelihood estimates if any applies.
 Source: slideplayer.com
Source: slideplayer.com
Ranked Vulnerability Risk Worksheet. 39 Ranked Vulnerability Risk Worksheet Asset Asset Impact Vulnerability Vulnerability Likelihood Risk-Rating Factor Customer service request via e-mail inbound 55 E-mail disruption due to hardware failure 02 11 Customer service request via e-mail inbound 55 E-mail disruption due to software failure 02 11 Customer order via SSL inbound. An approach to combining risk identification risk assessment and risk appetite into a single strategy. Managing Vulnerabilities and Applying Countermeasures Paper. Study Material Lecturing Notes Assignment Reference Wiki description explanation brief detail.
This site is an open community for users to submit their favorite wallpapers on the internet, all images or pictures in this website are for personal wallpaper use only, it is stricly prohibited to use this wallpaper for commercial purposes, if you are the author and find this image is shared without your permission, please kindly raise a DMCA report to Us.
If you find this site helpful, please support us by sharing this posts to your favorite social media accounts like Facebook, Instagram and so on or you can also bookmark this blog page with the title ranked vulnerability risk worksheet by using Ctrl + D for devices a laptop with a Windows operating system or Command + D for laptops with an Apple operating system. If you use a smartphone, you can also use the drawer menu of the browser you are using. Whether it’s a Windows, Mac, iOS or Android operating system, you will still be able to bookmark this website.





